The New Age of Intelligence
In 2025, the world is more connected than at any point in human history. Every minute, millions of posts, images, videos, searches, and conversations flow across the digital landscape, creating a constantly expanding map of human behaviour.
Each action leaves behind tiny, scattered traces: a location tag, a username, a comment, a transaction trail, a public document upload. Individually, they seem insignificant. Together, they form one of the largest intelligence reservoirs ever created.
Over 6 billion people use the internet worldwide, giving rise to an unprecedented volume of publicly accessible data. Every one of these interactions: whether a tweet, a news update, a forum discussion, or a satellite image, becomes a small piece of a much bigger puzzle.
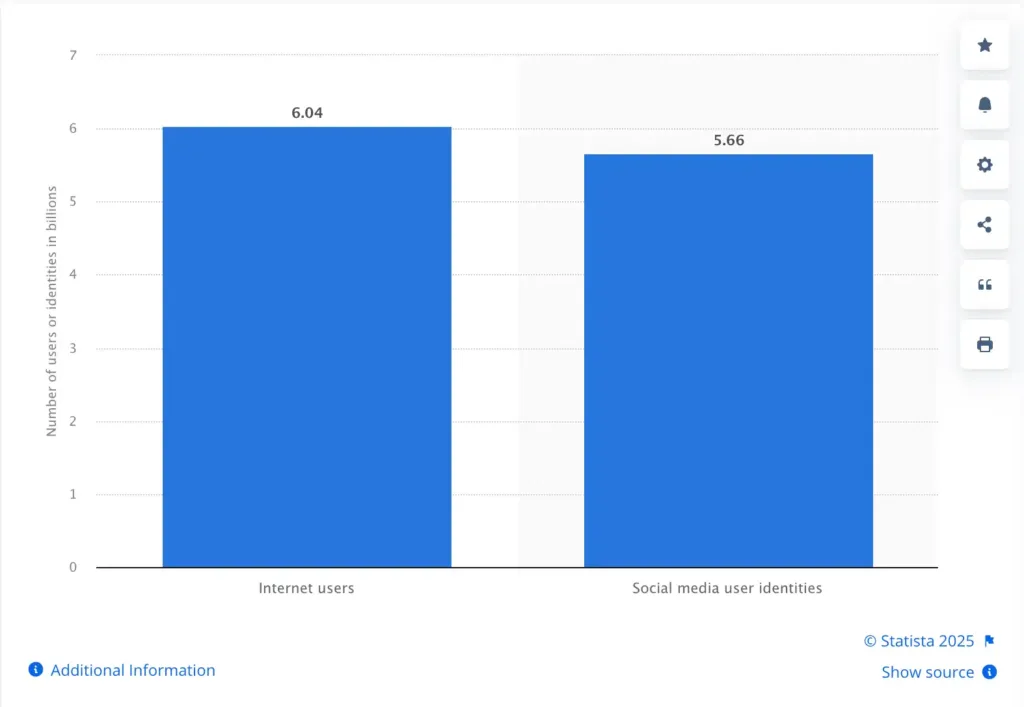
Source: Statista
This explosion of open information has transformed how nations defend themselves, how organisations assess risk, how journalists investigate stories, and how security teams anticipate threats. The stakes are higher than ever.
Key Takeaways
- OSINT is now a core intelligence discipline, critical for cybersecurity, law enforcement, counterterrorism, and geopolitical monitoring.
- The shift from manual monitoring to AI-powered OSINT enables real-time insights, predictive alerts, and contextual intelligence at scale.
- OSINT sources span the surface web, deep web, dark web, social media, and global RSS feeds, offering unmatched visibility.
- Modern OSINT requires multi-format data ingestion, cross-platform correlation, multilingual analysis, and automated entity resolution.
- AI capabilities — including sentiment analysis, image analysis, trend detection, and predictive modelling — greatly enhance OSINT accuracy and speed.
- Innefu’s Innsight offers sovereign, end-to-end OSINT capabilities aligned with the needs of defence, intelligence, and law-enforcement agencies.
- As threats become more hybrid and fast-moving, OSINT is becoming a strategic advantage, not just an investigative tool.
A World Defined by New-Age Threats

From misinformation campaigns shaping public opinion to cybercriminals coordinating attacks across social platforms…
From geopolitical tensions amplified by real-time digital chatter to hybrid warfare where narratives, influence, and information are as critical as physical capabilities.
Modern conflicts and security challenges now unfold in the open: on social media, public forums, news sites, and increasingly, the dark web. Threats no longer hide in shadows; they hide in plain sight, buried under layers of noise.
And this is exactly why Open-Source Intelligence (OSINT) has become indispensable.
The Paradox of the Information Age
Despite having more data available than any other generation before us, organisations often struggle to answer the most fundamental questions:
- What signals matter?
- Which conversations indicate emerging threats?
- What narratives are gaining traction?
- How do you distinguish between noise and intelligence?
Because data ≠ intelligence.
Not until it is collected, processed, analysed, and contextualised.
This is where OSINT enters the picture, turning the world’s open data into decision-ready insights.
Types of Open Sources Used in OSINT
Open-Source Intelligence draws its power from the vast amount of information publicly accessible across different layers of the internet. While OSINT can be sourced from thousands of platforms and repositories, the ecosystem can be broadly classified into 5 major categories. Each one offers unique visibility into events, actors, and digital behaviour.
1. Social Media Sources (SOCMINT)
Social platforms generate some of the richest and fastest-moving social media intelligence available today.
Key platforms:
- X (formerly Twitter)
- YouTube
- Telegram
- Regional platforms like ShareChat, TikTok, Weibo, etc.
SOCMINT enables:
- Event monitoring
- Behaviour and network mapping
- Narrative tracking
- Sentiment analysis
- Identification of fake accounts or coordinated campaigns
2. Deep Web
The deep web consists of online content not indexed by search engines but still openly accessible. No hacking or intrusion is required, just the right tools and permissions.
Examples of deep web sources:
- Academic databases
- Legal and court records
- Subscription-based industry reports
- Archived documents
- Public but unindexed search portals
- Public records requiring specific queries
3. Dark Web
The dark web is a restricted part of the internet accessible via tools like TOR. While unindexed, it still qualifies as open-source when accessed legally and without breaching systems.
Using dark web aggregators, analysts can identify:
- Illegal trade and marketplaces
- Leaked or stolen databases
- Threat actor discussions
- Malware/tool sales
- Early signals of cyberattacks or planned operations
4. Surface Web
The surface web includes everything indexed by standard search engines and accessible without special tools or credentials. Common surface web sources include:
- Public websites
- News portals
- Blogs, discussion forums, and community pages
- Public-facing corporate websites
- Government announcements and press releases
Search engines like Google, Bing, DuckDuckGo, etc. act as gateways, helping analysts scan, filter, and explore public content.
5. RSS Feeds (Cross-Geography Monitoring)
While often overlooked, RSS feeds are an essential OSINT source for structured media monitoring.
Analysts track:
- News outlets across multiple geographies
- Regional events
- Crisis alerts
- Policy updates
- Highly localised reporting
What Does OSINT Actually Help Uncover?

Below are practical, real-world scenarios that show OSINT in action:
1. Tracking Extremist Narratives
Analysts monitor:
- Hashtag spikes
- Encrypted-channel spillover content
- Recruitment patterns
- Group migration across platforms
This helps agencies detect radicalisation pipelines early.
2. Identifying Fake Accounts & Influence Operations
AI-enhanced OSINT tools detect:
- Coordinated posting patterns
- Bot networks
- False identities
- Manipulated images/videos
This is crucial during elections, crisis events, and geopolitical escalations.
3. Corporate Reputation & Brand Monitoring
Businesses use OSINT to track:
- Emerging negative narratives
- Viral misinformation
- Customer sentiment
- Activist mobilisation
Protecting brand trust requires early awareness.
4. Cyber Reconnaissance & Attack Surface Mapping
Cyber teams analyze:
- Exposed credentials on dark web
- Unpatched systems visible online
- Threat actor discussions
- Leaked PII
This enables early-warning before attacks occur.
OSINT is no longer optional. For modern organisations, government agencies, and security teams, it is the first line of intelligence that reveals what’s happening in the world — in real time, from open data.
OSINT vs. Other Intelligence Disciplines
To truly understand the value of OSINT, it helps to see how it fits within the wider intelligence ecosystem. Modern intelligence gathering isn’t about one method replacing another, it’s about multiple streams working together to create a complete picture.
Below is a clear explanation of how OSINT differs from traditional intelligence types.
1. OSINT vs HUMINT (Human Intelligence)
HUMINT involves gathering information through human sources: interviews, informants, undercover operations, field agents.
OSINT, in contrast, relies on:
- publicly available data
- digital footprints
- open platforms
- surface/deep/dark web sources
- social media activity
Key Differences
| OSINT | HUMINT |
|---|---|
| Data from open, digital, and public sources | Information from human interactions |
| Low-risk, non-intrusive | Higher operational risk |
| Scalable and fast via automation | Limited by human factors |
| Useful for broad trend identification | Useful for intent, insider knowledge |
2. OSINT vs SIGINT (Signals Intelligence)
SIGINT involves intercepting communications: radio signals, encrypted messaging, electronic emissions.
It often requires special equipment and legal authorizations.
OSINT, on the other hand, does not intercept anything. It uses freely accessible information.
Key Differences
| OSINT | SIGINT |
|---|---|
| No interception required | Involves capturing communications |
| Legally simpler, open-source | Strict legal frameworks |
| Scalable with automation | Resource-heavy |
| Focused on what people share publicly | Focused on what is communicated privately |
3. OSINT vs IMINT (Imagery Intelligence)
IMINT largely involves analyzing satellite images, drone visuals, or reconnaissance photography.
OSINT may include open satellite imagery (from platforms like Sentinel Hub, NASA Worldview, or commercial providers), but also pulls information from:
- news reports
- social media photos
- geotagged images
- public camera feeds
- crowd-sourced mapping
Key Differences
| OSINT | IMINT |
|---|---|
| Multi-source: text, video, social media, imagery | Primarily satellite/drone imagery |
| Often lower resolution or open-access | High-resolution, specialized tools |
| Wider context from multiple sources | Detailed visual analysis |
Learn more about Multi-source Intelligence.
How OSINT Complements Classified Intelligence
In today’s environment, OSINT has become a force multiplier for national security, law enforcement, and cyber defence.
It provides:
- early signals before threats escalate
- contextual insights around people, organisations, events
- verification for classified findings
- speed, especially during fast-moving incidents
- legally accessible intelligence agencies can use instantly
Classified intelligence reveals what is hidden. OSINT reveals what is overlooked. Together, they create a complete intelligence picture.
The OSINT Intelligence Cycle
Modern OSINT follows a refined, five-stage intelligence cycle designed to help agencies move from scattered public data to structured, actionable intelligence. Each stage brings clarity, reduces noise, and ensures that insights are operationally relevant.
1. Planning & Direction
The process begins with clearly defining what intelligence is needed and why.
Key elements include:
- Identifying mission objectives (e.g., tracking narratives, mapping networks, understanding event timelines).
- Establishing scope: geography, languages, timeframes, and entities of interest.
- Determining constraints and ethical guidelines governing the data to be collected.
This step ensures the OSINT effort is targeted, purpose-driven, and aligned with operational requirements.
2. Collection
At this stage, investigators gather relevant information from publicly accessible sources. Modern collection involves:
- Multi-source harvesting across web content, media reports, forums, surface/dark web sources, and publicly available datasets.
- Automated collection that scales with high-volume data environments.
- Respecting legal and platform-specific terms to ensure ethical and compliant acquisition.
The focus is not on “more data” but on “relevant, usable data.”
3. Processing
Raw data must be transformed into structured, analyzable intelligence. Processing typically includes:
- Normalization: Standardizing formats across text, images, and metadata.
- Translation: Converting multilingual sources into a common language for analysis.
- Media extraction: Parsing videos, images, and audio into searchable components.
- Noise removal: Eliminating duplicates, spam, and irrelevant chatter.
This step ensures that analysts are working with clean, high-quality information.
4. Analysis
This is where OSINT becomes actionable. Analysts apply reasoning and analytical frameworks to identify meaning within the processed data. Core analytical tasks include:
- Pattern identification: Recognizing recurring attributes, behaviors, or signals.
- Link analysis: Mapping relationships between individuals, entities, events, or digital footprints.
- Sentiment and narrative analysis: Understanding how online communities perceive or discuss an issue.
- Temporal trend analysis: Studying how conversations, activities, or behaviors evolve over time.
The goal is to convert data into insights that support decision-making.
5. Dissemination
Insights are packaged into clear, concise, and actionable formats for operational teams or decision-makers. Typical dissemination outputs include:
- Executive summaries
- Detailed intelligence reports
- Visual dashboards
- Alerts or periodic updates
The emphasis is on clarity, ensuring that complex findings are communicated in a format that is easy to interpret and act upon.
Real-World OSINT Applications Across Sectors

Open-source intelligence is no longer reserved for niche investigators. Today, OSINT drives decisions across national security, law enforcement, cybersecurity, finance, corporate risk, and emergency response. The examples below are designed to be timeless, safe, and technically accurate — ensuring the blog remains evergreen and reliable.
National Security & Strategic Intelligence
Governments use OSINT to build situational awareness and anticipate shifts in the global landscape.
How OSINT Helps
- Tracking geopolitical developments through official releases, public satellite imagery, and media reporting
- Monitoring border activities or infrastructure changes via publicly available geospatial data
- Studying open-source defense publications, trade announcements, and policy updates
- Understanding public sentiment during international crises
Law Enforcement & Public Safety
OSINT enhances investigative efficiency and provides early-warning capability without accessing any private or classified information.
How OSINT Helps
- Studying public social media chatter around events, gatherings, or emerging trends
- Identifying public posts that help piece together timelines during investigations
- Monitoring open forums for coordinated harmful activity
- Using public records (tenders, regulatory data, press releases) to map organizational activity
Cybersecurity & Threat Intelligence
Cyber teams rely on OSINT to identify risks before they escalate.
How OSINT Helps
- Monitoring public discussions about vulnerabilities
- Tracking mentions of malware or exploit kits in open sources
- Spotting leaked credentials on open breach repositories
- Identifying impersonation attempts or fake domains
- Understanding threat actor narratives circulating in open forums
Corporate & Competitive Intelligence
Businesses increasingly use OSINT to stay informed, compliant, and competitive.
How OSINT Helps
- Monitoring industry trends, competitor announcements, and customer sentiment
- Analyzing corporate registries for ownership changes
- Evaluating supply-chain risks through public tenders and filings
- Identifying brand impersonation or fake profiles online
Financial Fraud & Risk Monitoring
Financial institutions use OSINT to complement internal fraud-detection systems and risk scoring.
How OSINT Helps
- Studying public financial disclosures and compliance flags
- Detecting early signals of scams via open discussions or customer complaints
- Understanding cross-platform activity patterns linked to fraudulent behavior
- Using news portals to track regulatory actions and high-risk developments
Crisis Response & Disaster Intelligence
During emergencies, open data becomes indispensable for rapid decision-making.
How OSINT Helps
- Public satellite imagery to assess flood, fire, or storm damage
- Real-time public social media updates for on-ground conditions
- Official announcements from local authorities
- RSS feeds from news agencies and weather services
Due Diligence & Background Verification
OSINT helps organizations vet individuals, partners, or customers without accessing private or sensitive information.
How OSINT Helps
- Reviewing publicly available professional histories
- Checking open legal databases for relevant filings
- Validating identity signals from open digital footprints
- Analyzing press coverage, interviews, or public statements
Each sector uses OSINT differently, but the underlying principle remains the same: Convert publicly available data into clear, actionable intelligence.
OSINT Techniques: How Modern Open-Source Intelligence Works
OSINT is more than searching the internet. It uses structured, ethical methods to collect and analyze publicly available information. These methods fall broadly into three collection models: passive, semi-passive, and active, and each includes a range of practical intelligence techniques used by analysts today.

OSINT Collection Models:
1. Passive Collection
The safest and most widely used OSINT category.
Passive OSINT collects information without ever touching or interacting with the target system. It relies purely on publicly available data.
Examples of passive OSINT:
- Scraping public websites
- Collecting publicly shared posts from open social media sources
- Accessing open APIs where data is publicly intended (e.g., Twitter/X, news APIs)
- Monitoring RSS feeds from news agencies
- Reading public domain databases, reports, filings
- Searching through deep web portals that require only queries, not authentication
Why it’s preferred:
It is undetectable, anonymous, and completely safe when performed ethically.
2. Semi-Passive Collection
Often used in cybersecurity-focused investigations. Semi-passive OSINT technically interacts with the target’s system, but in a manner that resembles normal internet traffic, making it minimally invasive and often undetectable.
Examples of semi-passive OSINT:
- Running basic scanners that mimic standard web requests
- Checking server headers or SSL certificates
- Observing DNS records or subdomains
- Gathering metadata through standard network reconnaissance
Why it matters:
It provides environmental intelligence (infrastructure, exposure, public-facing services) without aggressive probing.
3. Active Collection
The most intrusive form, and generally avoided in ethical OSINT engagements.
Active collection interacts directly with a system to extract information. This type of collection can be logged, flagged, or blocked by the target’s firewalls, IDS, or IPS.
Examples of active OSINT techniques:
- Scanning open ports
- Probing web applications for publicly exposed vulnerabilities
- Running traceroutes that hit the target infrastructure
- Attempting interactions that may generate logs
- Social engineering attempts to elicit information
How AI is Transforming OSINT in 2025
For years, OSINT relied heavily on manual effort, analysts sifted through posts, verified images, correlated identities, and tracked narratives by hand. But the scale of today’s open-source data has made that approach impossible. With billions of posts, images, transactions, and discussions generated daily, AI has become essential for modern OSINT.

The transformation isn’t futuristic or speculative, it’s already happening through well-established AI capabilities that are widely used across industries.
Below are the macro trends shaping OSINT in 2025.
1. AI for Automated Summarization & Information Extraction
Large Language Models (LLMs) and NLP tools are now widely used to:
- summarise long news articles
- extract key entities (names, events, places)
- identify relationships between entities
- detect sentiment or tone
- filter irrelevant content
These capabilities are already standard across enterprise-grade platforms and research tools.
For OSINT analysts, this means:
- faster triage of huge data sets
- instant extraction of actionable intelligence
- reduced manual reading time
2. Automated Link Analysis & Entity Mapping
AI-powered graph analysis tools now help investigators automatically:
- identify recurring connections between people, organisations, locations
- visualise communication or influence networks
- detect hidden relationships that humans might miss
Graph algorithms and clustering models are widely used in cybersecurity, law enforcement, and financial intelligence — making them an essential part of modern OSINT workflows.
Why it matters:
Analysts can move from raw data → relationship insights in seconds.
This is also where platforms like Innefu’s Innsight provide a high-value edge through automated link charts and AI-based correlation engines.
3. Real-Time Narrative & Trend Detection
AI models can analyse large volumes of public posts in real time to detect:
- sudden keyword spikes
- coordinated posting patterns
- misinformation or bot-like behaviour
- sentiment shifts
- emerging public narratives
Trend detection using machine learning is now a core part of OSINT, marketing analytics, counter-misinformation, and geopolitical monitoring.
Example:
A sudden surge in specific hashtags or location-based chatter can indicate protests, unrest, or coordinated campaigns. Innsight’s trend analytics and narrative clustering follow these exact principles, giving agencies early situational awareness.
4. AI-Powered Image & Video Forensics
Computer vision and ML have dramatically improved:
- object detection
- face identification
- geolocation support
- tamper detection
- reverse image matching
- image clustering
These capabilities are widely documented in computer vision research and used across defence, security, fraud detection, and media verification.
For OSINT, it means analysts can now:
- validate authenticity faster
- extract details from low-quality media
- detect reused or misleading footage
- identify landmarks or objects automatically
This makes verification, once the most time-consuming task, significantly more efficient.
5. Predictive Signals Derived From Open Data
AI can detect early-warning indicators by analysing patterns over time, such as:
- shifts in local sentiment
- unusual increases in coordinated posts
- rapid follower growth in newly created accounts
- abnormal conversation clusters
- location-based behaviour changes
These predictive insights are already widely used in:
- cybersecurity threat intelligence
- public safety monitoring
- geopolitical risk analysis
Platforms like Innefu’s Innsight use similar principles to generate early alerts on emerging threats, unlawful gatherings, propaganda shifts, or coordinated campaigns — always using open-source, publicly available data.
Why Modern Agencies Need AI-Driven OSINT
The intelligence landscape has changed more in the last five years than in the previous fifty. Open-source data, once considered supplementary, has now become a decisive element of national security and law enforcement operations.
From global misinformation campaigns to flash-mob protests, from cyber extortion groups to cross-border propaganda networks, today’s threats begin in the open.

But the challenge is not access to information; it is the scale, speed, and complexity of it.
Modern agencies need OSINT ecosystems that can handle:
- multi-format data ingestion (text, images, deep web, dark web, RSS feeds, social media)
- contextual correlation across time, entities, and sources
- real-time narrative monitoring
- predictive intelligence to flag emerging threats
- low-noise, high-signal analysis
- sovereign, secure, on-premise AI for national agencies
This is no longer optional, it’s operational necessity.
Innsight by Innefu: AI-Powered OSINT for the Modern Intelligence Era
In this new intelligence paradigm, Innefu’s Innsight has emerged as one of India’s most advanced, sovereign OSINT platforms, built ground-up for defence, intelligence, and law enforcement agencies.
It embodies every capability modern OSINT requires:
1. Multi-Source Data Fusion: Surface, Deep, Dark Web + Social + RSS Feeds
Innsight consolidates intelligence across:
- Surface Web (search engines, news, blogs, public websites)
- Deep Web (unindexed data portals, academic records, registries)
- Social Media (Facebook, Instagram, X/Twitter, YouTube, regional platforms)
- Dark Web (leak forums, marketplaces, threat actor chatter)
- RSS Feeds (multi-country newspapers and local news ecosystems)
This breadth ensures agencies see the complete intelligence picture, not fragmented clues.
2. Event-Specific Intelligence & Situational Awareness
When a protest, mass gathering, or sensitive event begins to trend online, Innsight:
- monitors emerging narratives
- detects early indicators of escalation
- identifies origin points of unrest
- highlights coordinated hashtags/accounts
- correlates chatter with sentiment shifts
Agencies gain real-time situational awareness, allowing timely deployment and risk mitigation.
3. Advanced Profiling & 360-Degree Entity Intelligence
Modern threats are interconnected. Innsight consolidates entity data from multiple platforms to create:
- individual profiles
- organization footprints
- relational networks
- influence chains
- communication patterns
A 360-degree view reveals hidden connections, enabling agencies to disrupt networks early.
4. Trend, Sentiment & Narrative Analysis (60+ Analytical Widgets)
With customizable AI-driven dashboards, analysts can monitor:
- sentiment spikes
- emerging narratives
- propaganda patterns
- misinformation bursts
- cross-border influence campaigns
This is crucial for counter-disinformation, public safety monitoring, and national security.
5. Predictive Analytics & Early Warning Signals
Innsight’s predictive engine uses historical and real-time patterns to forecast:
- potential unrest
- vulnerable hotspots
- narrative escalation
- coordinated campaigns
- extremist recruitment attempts
Modern threats require pre-emption, not reaction, and Innsight gives agencies that head start.
6. Image & Multimedia Analysis
With built-in computer vision capabilities, Innsight can:
- identify individuals across trending images
- detect objects or symbols linked to events
- validate media sources
- extract metadata
- assist with cross-platform verification
A critical capability when misinformation spreads visually.
7. Alerting & Intelligence Dissemination
Analysts can configure:
- keyword-based alerts
- narrative alerts
- entity alerts
- dark web activity alerts
Notifications are delivered via platform, email, or SMS, ensuring no early signal is ever missed. Reports and widgets can be exported in PDF, DOC, CSV, enabling seamless briefing and case reporting.
To conclude: OSINT is No Longer Optional, It’s Foundational
The world is experiencing an unprecedented explosion of open data. Every post, image, location tag, leaked database, and online narrative adds a new layer to the global intelligence fabric. But the true value of OSINT doesn’t come from the volume of this data, it comes from the ability to interpret, correlate, and act on it.
From countering misinformation to identifying extremist networks, from predicting unrest to strengthening cybersecurity posture, OSINT has evolved into a core pillar of national security, public safety, and digital resilience.
But modern challenges demand modern solutions. This is why AI-driven, multi-source OSINT — the kind that can understand patterns, detect threats early, and provide real-time situational awareness — has become essential for defence, intelligence, and law-enforcement agencies worldwide.
In this landscape, Innefu’s Innsight stands as a strategic force multiplier. Purpose-built for large-scale, sovereign intelligence operations, it allows agencies to see deeper, respond faster, and stay ahead of adversaries across borders, domains, and digital ecosystems.
The future of intelligence is open-source. And the agencies that embrace AI-powered OSINT today will define the security outcomes of tomorrow.
FAQs – Frequently Asked Questions
1. What is OSINT in simple terms?
OSINT (Open-Source Intelligence) refers to collecting and analyzing information from publicly available sources — such as websites, social media, news, deep web portals, and open databases — to generate actionable intelligence.
2. What are the main sources of OSINT?
Common OSINT sources include the surface web, deep web, dark web, social media platforms, and RSS feeds from global news publications.
3. How is OSINT different from traditional intelligence?
Traditional intelligence often relies on classified or covert methods.
OSINT uses publicly available information, making it:
- legally simpler
- faster to collect
- scalable across digital platforms
This makes OSINT ideal for early threat detection.
4. Is OSINT legal?
Yes. OSINT uses data that is publicly accessible without breaching security, privacy, or hacking laws.
Ethical collection and compliance are essential.
5. How do law-enforcement agencies use OSINT?
Agencies use OSINT for:
- tracking suspects or networks
- identifying misinformation
- monitoring protests or unrest
- uncovering extremist activities
- threat forecasting
- cyber reconnaissance
Tools like Innsight support these workflows at national scale.
6. How does AI improve OSINT capabilities?
AI enhances OSINT by enabling:
- automated data collection
- entity profiling
- trend/sentiment analysis
- image and video analysis
- real-time alerts
- predictive threat modelling
This helps analysts work faster with higher accuracy.
7. What is the difference between OSINT and SOCMINT?
SOCMINT (Social Media Intelligence) focuses specifically on social platforms such as X, Facebook, Instagram, Telegram, and YouTube. OSINT covers all open sources, including web pages, deep web portals, dark web forums, databases, and social media.
8. What is an OSINT tool?
An OSINT tool is a platform that automates the collection, monitoring, analysis, and reporting of open-source data.
For example, Innefu’s Innsight helps agencies track narratives, profile entities, detect emerging threats, and gather real-time intelligence from multi-format sources.
9. Can businesses use OSINT?
Yes. OSINT is widely used in:
- brand reputation monitoring
- competitive intelligence
- due diligence
- cyber risk assessment
- fraud detection
10. Why is OSINT becoming so important today?
Because modern threats: misinformation, cyberattacks, extremist coordination, protests, geopolitical tensions, start in the open. OSINT provides early signals long before traditional intelligence systems detect them.





