India’s banking system lost ₹36,014 crore to fraud in FY 2024-25, a 194% jump over the prior year – Risk Management Association of India. And when RBI broke down where those losses came from, the answer was unambiguous: loan scams caused the heaviest rupee losses. Not card fraud. Not internet banking. Loans.
That is what makes loan fraud so damaging, and so difficult to stop. It does not look like fraud when it walks in. It looks like a customer.
This guide covers exactly what loan fraud is, how the three most common typologies actually work, why manual review processes fail against them, what AI-powered detection does differently, and what the full detection stack looks like in practice. No theory. No generic advice. Just what the problem actually is and how to solve it.
Key Takeaways
- Loan fraud costs Indian banks ₹36,014 crore in FY25 alone, a 194% year-on-year increase, with loan scams as the primary driver of rupee losses.
- Three typologies cause the majority of application-stage loan fraud, identity reuse, rejected applicant re-entry, and organised ring fraud, and all three are invisible without automated detection.
- Manual review cannot catch what is distributed across branches and lenders, a face that appeared in a rejected application at another branch looks like a fresh applicant without cross-branch photo matching.
- The rejected application repository is your highest-value fraud asset, and most institutions do not use it systematically.
- AI detection works across two engines simultaneously, facial biometrics matching and OCR document cross-check, combining both produces a composite risk score that neither alone can generate.
- RBI’s revised Fraud Risk Management Directions (July 2024) mandate Early Warning Systems, making automated fraud detection at origination a regulatory obligation, not just a best practice.
- Detection speed matters as much as detection accuracy, a fraud alert fired within seconds of application submission stops disbursement; a flag raised three days later does not.
What is Loan Fraud, And Why India is Particularly Exposed
Loan fraud is the deliberate misrepresentation of identity, income, or intent in a loan application to obtain credit that would not otherwise be sanctioned.
It’s not a new problem. But three things have made it significantly worse in the last five years in India:
The volume explosion in digital lending
When loan origination happens in a branch, a human being meets the applicant. There is at least a baseline of visual verification. When origination happens through a mobile app, a DSA channel, or a digital-first NBFC, that baseline disappears. The fraudster is never in the room. They just need to upload documents and a photograph.
The fragmentation of the lending market
India now has hundreds of NBFCs, dozens of digital lenders, fintech platforms, co-lending arrangements, and multiple banking channels, all originating loans. A fraudster rejected by one lender can immediately apply to another. Without cross-institution information sharing at the speed of origination, rejection at one place is not a barrier to success elsewhere.
The sophistication of document manipulation
Forged salary slips, manipulated bank statements, fabricated ITRs, Aadhaar numbers submitted with altered photographs, the quality of fraudulent documentation has improved materially as digital editing tools have become accessible. What would have required specialist forgery skills a decade ago can now be done on a smartphone.
The result is an environment where loan fraud is more scalable, more accessible, and harder to detect through manual processes than at any prior point in India’s lending history.
The Three Typologies That Drive Application-stage Loan Fraud
Understanding how loan fraud actually works, not in theory, but in the specific patterns that show up in loan origination pipelines, is the starting point for building detection capability that actually catches it.
Typology 1: Identity Reuse, Same Face, Different Names
Here is what this looks like in practice.
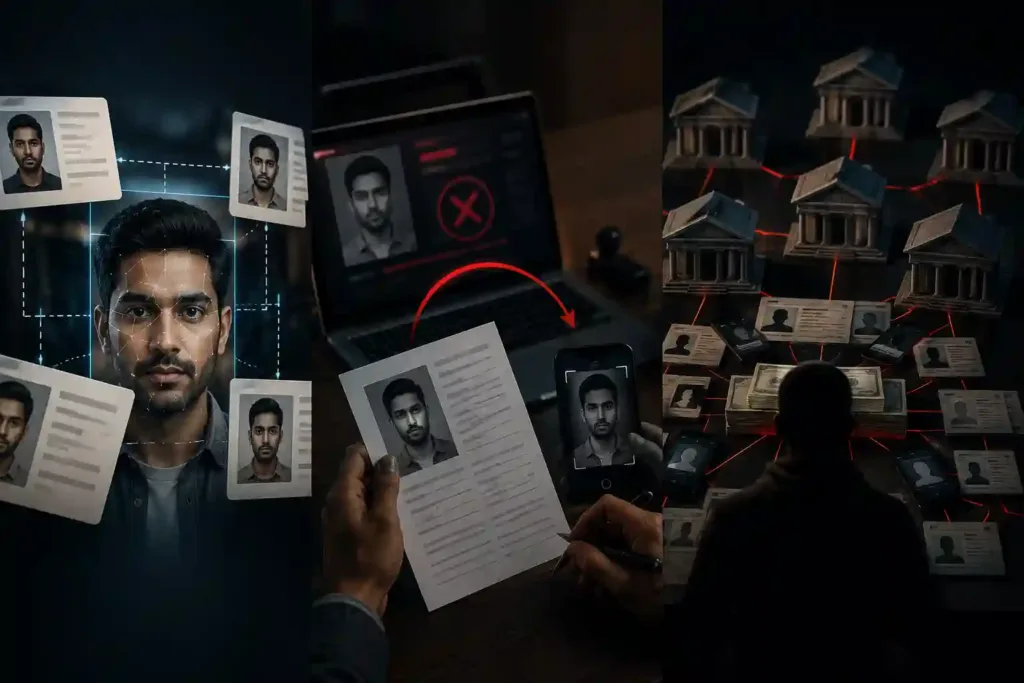
A fraudster has one photograph. They submit loan applications under four different names, Ramesh Kumar, R.K. Sharma, Ramesh K., R. Kumar, across multiple branches or multiple lenders. The application details are different enough that no individual form triggers a flag. The income is inflated but not absurdly so. The address is plausible. The PAN card looks real.
To the loan officer at each branch, this is a first-time applicant. To the loan system, unless it has cross-branch photo matching, each application looks entirely independent.
The fraud succeeds at multiple lenders simultaneously. Multiple loans are disbursed to what is effectively the same person, whose actual creditworthiness was never assessed because their real identity was never established.
This is the most common form of application-stage identity fraud. It exploits the fundamental limitation of manual review: a human being can only compare a face against their own memory of faces they have personally seen. They cannot compare it against ten thousand rejected applications from branches they have never visited.
Typology 2: Rejected Re-entry, Rejected Yesterday, Applying Today
A loan application is rejected. The rejection reasons might be fraud indicators, income inflation that doesn’t match the salary slip, a PAN number that has been used before, an address that appears on a blacklist. The system works. The fraud is caught.
Forty-eight hours later, the same person applies again. Different branch. Different channel. Slightly modified details, different spelling of the name, updated address, new phone number. The face is the same. The fraud intent is the same.
If the institution has not retained the rejected application photograph and made it searchable at the point of the new application, the re-entry is invisible. The same person who was caught yesterday becomes a fresh applicant today.
This is arguably the most preventable form of loan fraud, the information to stop it already exists in the lender’s own system. What is missing is the ability to use it in real time at origination.
Typology 3: Organised Ring Fraud, One Operation, Many Loans
This is the most damaging typology in terms of total exposure, and the most sophisticated in terms of how it is organised.
A loan fraud ring recruits or fabricates multiple applicants, some real individuals acting as mule borrowers, some synthetic or fictitious identities, and submits simultaneous applications to multiple lenders. The photographs, mobile numbers, addresses, and employer details are coordinated: the same phone number appears on applications under different names, the same employer ID is used for multiple employees, the same photograph appears with different personal details across different lenders.
No single institution sees the full picture. Each lender sees only the applications submitted to them. The coordinated nature of the ring, which is what makes it a ring, is only visible when you look across lenders, across branches, and across documents simultaneously.
This is the typology that causes the largest losses in absolute terms. A coordinated ring can generate crores in fraudulent disbursements across a period of days before any single lender has assembled enough information to identify what is happening.
Why Manual Review Fails Against All Three
Manual review is not a broken process. For the task it was designed for, a loan officer assessing one application at a time, in person, with the applicant in front of them, it is reasonable.
The problem is that none of the three typologies above are visible to a process that works one application at a time.
Identity reuse is invisible without cross-application photo matching
A loan officer cannot compare a new applicant’s photograph against thousands of prior rejected applications from memory. They can only compare against what is in front of them, and what is in front of them looks fine.
Rejected re-entry is invisible without a searchable cross-branch rejection history
If the rejection is recorded in a branch-level system that the next branch has no access to, the information that should stop the re-entry does not reach the person who needs it.
Ring fraud is invisible without cross-application field deduplication at scale
The signal that identifies a ring, the same mobile number appearing on applications under three different names in the same week, is only visible if all three applications are in the same searchable database and that database is queried for overlaps in real time.
Manual review, by its nature, cannot do any of these three things. It works on one application. It works in one branch. It works at one moment in time. Fraud does not.
How AI-powered Loan Fraud Detection Actually Works
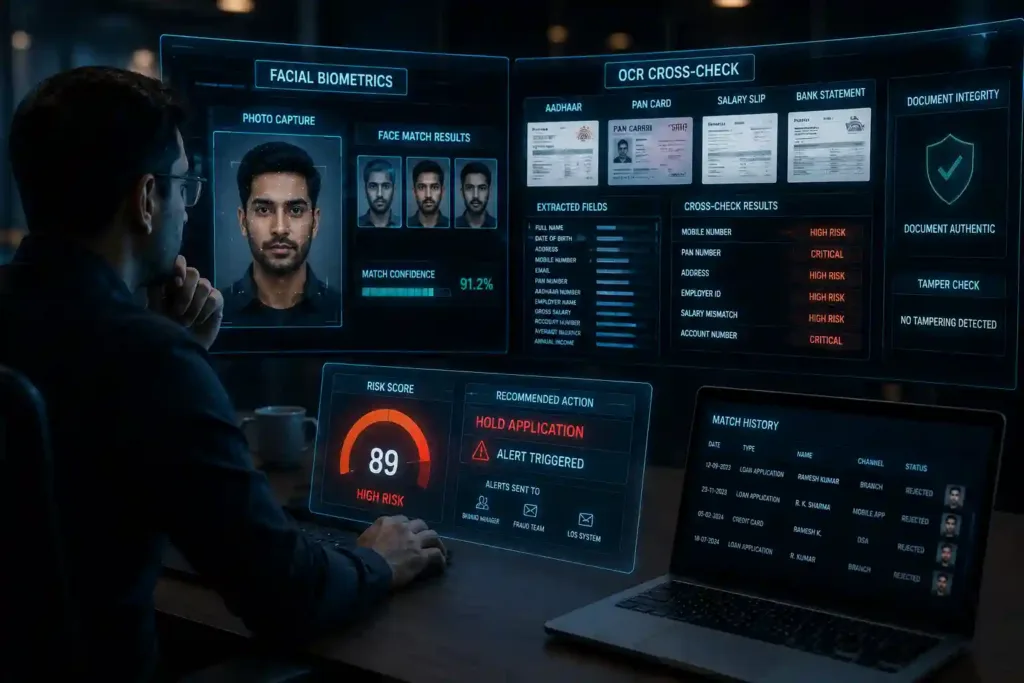
AI-powered loan fraud detection operates across two engines simultaneously. Neither alone is sufficient, the combination is what produces detection accuracy at origination speed.
Engine 1: Facial Biometrics, The Photo Matching Engine
When a loan application is submitted, through any channel, branch, mobile app, or DSA, the applicant’s photograph is immediately processed through a deep learning model that extracts a facial embedding: a mathematical representation of the face as a vector of numerical values.
This embedding is then compared against the entire historical photograph repository, every rejected application, every approved loan file, every NPA account, every credit card application, every KYC photo from account opening. The comparison happens against a vector database that can hold tens of millions of embeddings and return results in under 200 milliseconds.
If the same face appears in the database, under a different name, a different address, a different date of birth, the match is flagged immediately, with a confidence score and side-by-side visual evidence for the reviewing analyst.
Critically, the system works even with partial face obscuration, photograph filters, different lighting conditions, and photographs taken at different angles or different points in time. The embedding captures the underlying facial geometry, not the surface appearance of the photograph.
What this means in practice: a fraudster who submitted a rejected application two years ago, with a different name, at a different branch, looks identical to the system now. There is no gap in institutional memory.
Engine 2: OCR Cross-check, The Document Intelligence Engine
In parallel with photo matching, an OCR (Optical Character Recognition) engine processes every document submitted with the application, application form, Aadhaar card, PAN card, salary slip, bank statement, ITR or Form 16.
The engine extracts key fields from every document: full name, date of birth, address, mobile number, email, PAN number, Aadhaar number, employer name and ID, gross salary, account number, average balance, annual income.
These extracted fields are then cross-referenced against the historical application database, every prior application, regardless of the channel through which it was submitted.
The cross-check logic flags specific, high-risk patterns:
The same mobile number appearing under a different name is a HIGH risk flag. The same PAN under a different name is CRITICAL. The same address under a different name is HIGH. The same employer ID with a different employee name is HIGH. Declared income on the application form that does not match the extracted salary slip figure is HIGH. A reused account number is CRITICAL.
Beyond field matching, the OCR engine also performs document integrity checks, detecting signs of tampering through metadata analysis, font consistency checking, and comparison of declared field values against extracted values. A salary slip where the font of the salary figure is different from the surrounding text is a tamper indicator. An Aadhaar card where the extracted address does not match the address declared on the application form is a consistency failure.
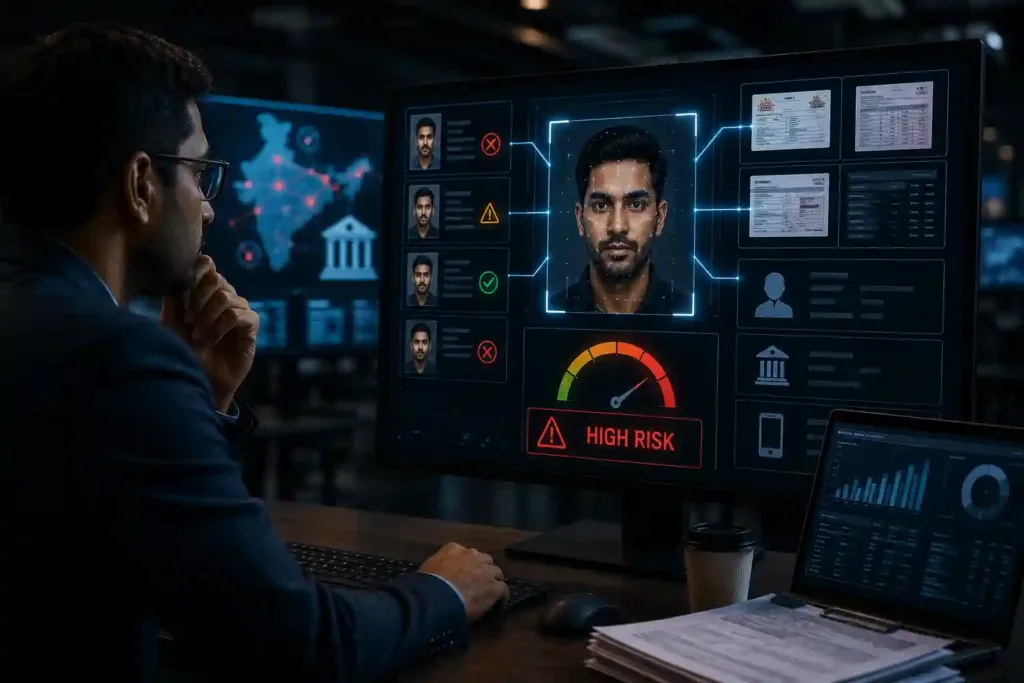
The Risk Score
The outputs of both engines, the face match confidence score and the OCR overlap signals, combine with application metadata into a composite fraud risk score. This score determines what happens next.
High-risk applications are held automatically and an alert is fired to the branch manager, fraud team, and loan origination system within seconds. The reviewing analyst sees a structured case: the side-by-side face match, the specific OCR fields that triggered flags, the match history showing where the same face or the same fields appeared before, and a recommended action.
The decision is still human. The information that makes that decision accurate is AI-generated, assembled in seconds, and presented in a format that a human analyst can act on immediately.
The Seven Alert Types, What Gets Flagged and Why

A well-configured loan fraud detection system generates specific, actionable alerts rather than generic “suspicious application” flags. Here are the seven alert types that matter most:
Duplicate Identity
The same person has submitted an application under a different name. Face match confidence above threshold, identity fields inconsistent with prior applications.
Rejected Re-Entry
The applicant appears in the rejected application repository. Previously turned down for fraud indicators; now reapplying with modified details.
Field Overlap
A shared PAN, mobile number, or bank account number appears under a different named applicant. Could indicate identity fraud or ring membership.
NPA Match
The applicant’s photograph or identity fields match a known defaulter or NPA account. Active defaulter attempting to re-enter the lending system under a modified identity.
Income Mismatch
Declared income on the application form does not match the income extracted from salary slip, Form 16, or ITR. Income inflation is one of the most common fraud enablers.
Document Tamper
OCR metadata analysis or font consistency checking has detected signs that a submitted document has been altered. The flag includes the specific document and the nature of the detected inconsistency.
Ring Member
The applicant shares fields, mobile number, address, employer ID, with one or more other current or recent applications, suggesting coordinated ring activity rather than isolated fraud.
Each alert type carries a severity level, Critical, High, or Medium, and routes to the appropriate review queue based on that severity.
The Data Sources That Make Detection Possible
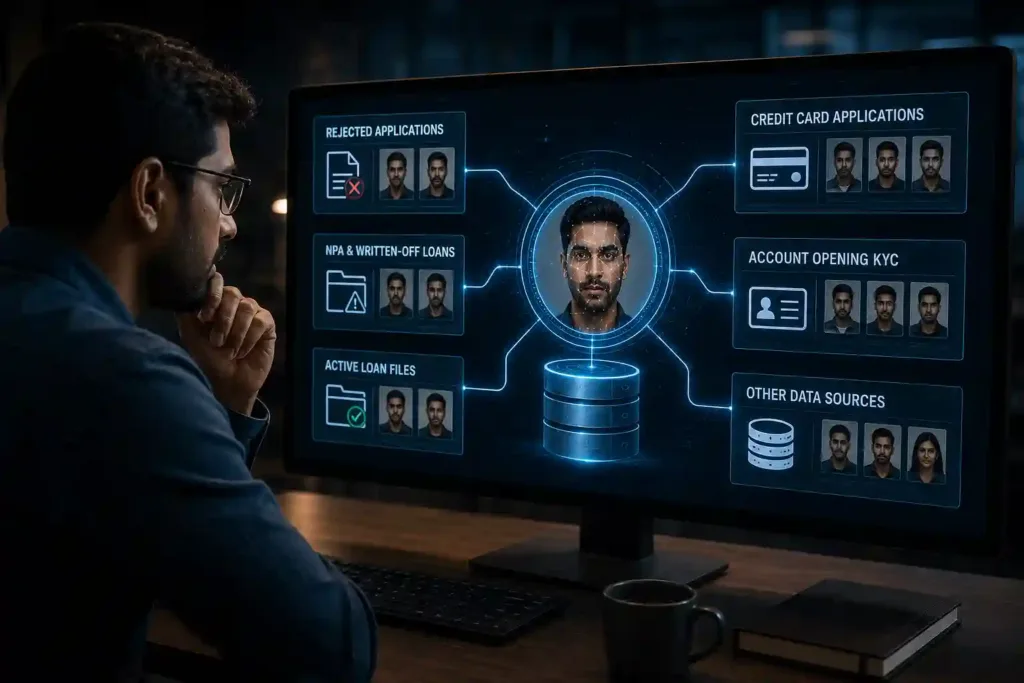
The quality of loan fraud detection is directly proportional to the breadth and quality of the historical data the system can search against. The photograph repository and field index are only as valuable as the sources feeding them.
The sources that matter most, in rough order of value:
Rejected Applications
The highest-value fraud repository an institution holds. Every application that was turned down for any reason, fraud indicators, credit failure, incomplete documentation, is a potential future match against a fraudster who will try again.
NPA and Written-Off Loan Files
Known defaulters and written-off borrowers are among the highest-risk re-entry profiles. Their photographs and identity fields must be searchable at origination.
Active Loan Files
Existing borrowers appearing in a new application under a different name or identity is a serious flag, both for internal fraud and for loan stacking across products.
Credit Card Applications
Cross-product identity checking catches fraudsters who have previously applied for or held credit cards under different identities.
Account Opening KYC
Savings and current account KYC photographs represent a significant identity baseline that most lenders do not currently use for loan origination fraud detection.
The common thread: every identity event, every application, every KYC, every account opening, should feed the photo repository and field index. The more complete the historical record, the more powerful the detection.
What to Look for When Evaluating a Loan Fraud Detection Solution
If you are assessing fraud detection platforms for your loan origination process, these are the questions that separate genuine capability from capability-sounding marketing:
What is the search speed across the full repository?
Detection that takes minutes is not real-time detection. A system that returns a match result in under 200 milliseconds across a repository of 10 million-plus records is operationally viable; anything slower creates a bottleneck in the origination flow.
Does it handle Indian document formats?
Aadhaar, PAN, salary slips in regional languages, bank statements from Indian banks, these are the documents your applicants submit. A system trained on Western document formats will have extraction accuracy gaps on Indian KYC documents.
How is the photo repository updated?
A static repository that is refreshed monthly is not adequate. The rejected application repository should be updated in real time, the moment an application is rejected, that photograph is searchable against the next incoming application.
What is the false positive rate?
A system that flags 40% of applications as suspicious is not a fraud detection system, it is a manual review generator. Ask for the specific false positive rate on production deployments, not on test data.
Does it produce evidence, not just scores?
A risk score tells you something might be wrong. Side-by-side face match evidence, with the specific OCR fields that triggered the flag and the historical application it matched against, tells you what is wrong and gives your analyst the information they need to make a decision.
Does it integrate with your LOS?
Fraud detection that exists outside the loan origination system creates a parallel process that gets bypassed under volume pressure. Integration with the LOS means detection happens automatically on every application without requiring a separate manual trigger.
Loan fraud will not be solved by asking loan officers to be more careful, adding more fields to the application form, or tightening income documentation requirements. Fraudsters adapt to all of these faster than institutions can implement them.
What actually works is detection that operates at the same scale and the same speed as the fraud, across every application, every channel, every branch, simultaneously, in real time. Detection that remembers every face it has ever seen and cross-references every field against every prior application the moment a new one arrives.
That is what AI-powered loan fraud detection delivers. And in the current regulatory environment, with RBI’s 2024 Fraud Risk Management Directions mandating EWS integration and ₹36,014 crore in banking fraud losses in a single year, it is not a technology investment that can be deferred.
Frequently Asked Questions
1. What is loan fraud?
Loan fraud is the deliberate misrepresentation of identity, income, or intent in a loan application to obtain credit that would not otherwise be sanctioned. In India, the most common forms involve fake or forged identity documents, inflated income through manipulated salary slips or ITRs, and organised rings that submit multiple coordinated applications across lenders. Loan fraud was the primary driver of bank fraud losses in India in FY 2024-25, accounting for the heaviest rupee losses in RBI’s annual fraud report.
2. What are the most common types of loan fraud in India?
The three typologies that cause the majority of application-stage loan fraud in India are identity reuse (submitting the same photograph under different names across branches or lenders), rejected applicant re-entry (reapplying with modified details after a prior rejection), and organised ring fraud (coordinated networks of mule borrowers submitting simultaneous applications with shared identity fields). Beyond these, income mismatch fraud, declaring inflated income not supported by actual salary slips, bank statements, or ITRs, and NPA re-entry fraud are significant contributors.
3. How do banks detect loan fraud in India?
The most effective loan fraud detection combines two approaches: facial biometrics photo matching, comparing the applicant’s submitted photograph against a repository of all prior applications using AI-powered face embedding, and OCR document cross-checking, extracting fields from all submitted documents and cross-referencing them against historical applications for field overlaps like shared PAN numbers, mobile numbers, or bank account numbers. A composite risk score from both engines generates a real-time alert at the point of origination before any disbursement decision is made.
4. What is the RBI requirement for loan fraud detection?
RBI’s revised Master Directions on Fraud Risk Management, issued in July 2024, mandate that banks and NBFCs implement Early Warning Systems (EWS) integrated with their Core Banking Solutions. These systems must proactively identify fraud risk indicators at the application stage. Red-flagged accounts must be reported to RBI’s CRILC platform within seven days. The directions apply to commercial banks, cooperative banks, regional rural banks, and NBFCs including housing finance companies.
5. Why is manual review insufficient for loan fraud detection?
Manual review works on one application at a time and is limited to what the reviewing officer can compare from memory and the information immediately in front of them. Identity reuse fraud, the same face submitting applications under different names at different branches, is invisible without cross-branch photo matching that no human can perform manually at scale. Rejected re-entry fraud requires a searchable cross-branch rejection history. Ring fraud requires real-time field deduplication across all current applications simultaneously. Manual review structurally cannot do any of these three things.
6. What is a loan fraud ring?
A loan fraud ring is an organised network of individuals, some real mule borrowers, some fictitious identities, who submit coordinated loan applications across multiple lenders simultaneously. The ring is identified by shared fields across applications: the same mobile number under different names, the same employer ID for different employees, the same address across multiple applicants. No single lender sees the full ring, each sees only the applications directed to them. Cross-application field deduplication and network analysis are required to identify ring membership.
7. How fast should a loan fraud detection system flag an application?
Detection must happen before the disbursement decision, which in many digital lending environments means within seconds of application submission. A well-configured system running facial biometrics matching against a repository of 10 million-plus records and OCR field cross-checking across all submitted documents should return a composite risk score and alert within seconds of the application being received. Detection that takes hours or days is forensic, not preventive.




