In modern investigations, the smartphone is often the most informative witness. From chat logs and photos to location traces and app artifacts, mobile devices reveal sequences of behaviour that can confirm alibis, map networks, and expose intent.
This guide walks through the investigator’s workflow, from lawful seizure to courtroom-ready reporting, explaining practical techniques, common pitfalls, legal safeguards, and new trends that accelerate time-to-insight.
The aim: provide investigators, legal teams, and forensic managers with an operational playbook grounded in accepted standards and best practices.
Key takeaways
- Treat the phone as a primary witness: document, preserve, and acquire thoughtfully.
- Choose acquisition methods based on device state, legal authority, and investigatory value – logical, file system, physical, cloud.
- Normalize timestamps and build a corroborated timeline using multiple sources (CDRs, CCTV, OSINT).
- Preserve auditability: hashes, tool validation, and analyst notes are essential for courtroom use.
- Use AI and integration to prioritize evidence, not replace human verification or legal safeguards.
The Smartphone as the modern “black box”
Unlike a decade ago, investigators now routinely reconstruct timelines and relationships from mobile artefacts that were never designed for forensic use.
The result is a shift: investigations start with the device and radiate outward – to call data records (CDRs), cloud backups, CCTV, and open-source intelligence (OSINT), creating a layered, corroborated picture of events. This device-centric reality is why mobile device forensics is not optional, but a core investigative capability.
High-level Investigative Workflow
Before the technical options come into play, investigators use a repeatable pipeline as their mental model:
- Identification & lawful seizure
- Preservation & isolation
- Data acquisition (logical, file system, physical, cloud)
- Parsing & normalization of artifacts
- Timeline reconstruction & correlation
- Link analysis & pattern detection
- Reporting, validation & courtroom readiness
A clear flowchart helps teams make rapid decisions on-scene and in the lab, which in turn preserves evidence integrity and speeds case resolution. Institutionalizing this flow aligns practice with guidance from forensic standards organizations.
Step 1 – Identification & Lawful Seizure
The moment a device is identified as potential evidence, two priorities take precedence: (a) legal authority and (b) meticulous documentation.
Legal authority
A lawful seizure often requires warrants, court orders, or well-established exceptions (exigent circumstances). Investigators should consult legal counsel or follow agency policy before accessing device contents. This early step protects admissibility later.
Document the device state
Photograph the device in place, note whether it’s powered on, and record visible notifications, SIM cards, and connected accessories. Capture observable identifiers – make, model, IMEI/MEID, and carrier, on the arrest/search form. These simple records are often decisive in court.
Step 2 – Preservation & Isolation: Preventing remote alterations
Mobile devices are networked devices, they can be remotely wiped, synced, or altered. Preservation techniques prevent such interference:
Faraday bags/signal-blocking
Placing a powered device inside an RF-shielding container prevents network-based changes (remote wipe, push notifications). Guidance from SWGDE and other authorities emphasizes correct use; e.g., put both device and charger inside the bag if you must keep it powered.
Power decisions
If a device is off, many guidelines recommend leaving it off and documenting that decision. If it’s on, depending on device type and agency policy, preservation may mean placing it in airplane mode, using a Faraday bag, or connecting to a controlled power source inside the shield.
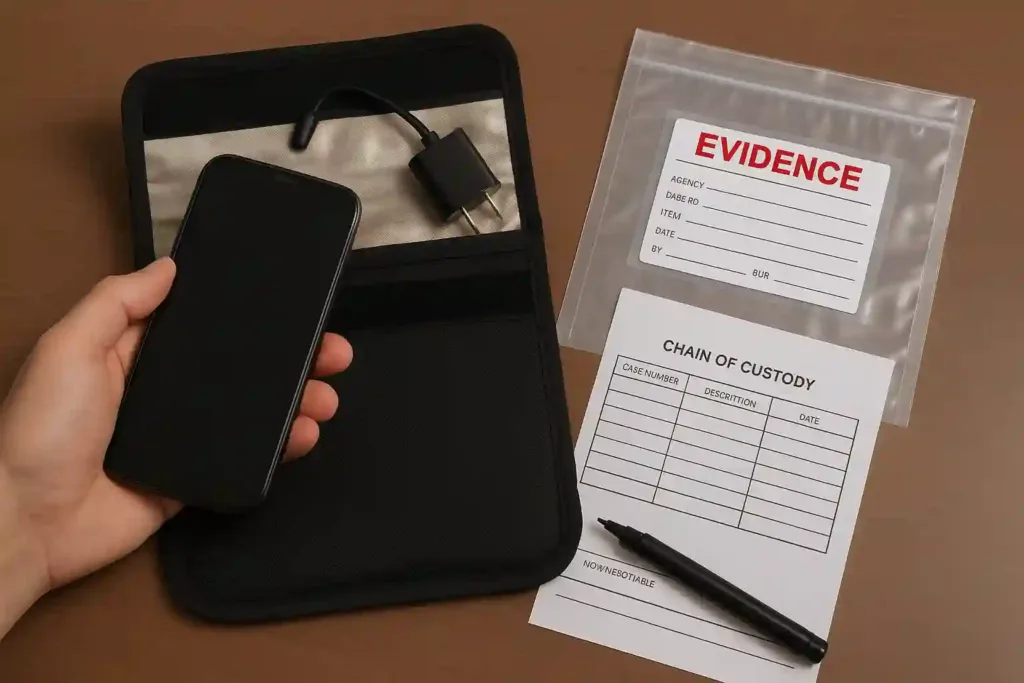
Packaging & chain of custody
Evidence packaging, anti-static measures, evidence labels, and a signed chain-of-custody log are non-negotiable, they preserve trust in the evidence from seizure through trial.
Step 3 – Data Acquisition: Choosing the right technique
Acquisition is the technical core of mobile forensics. The method chosen depends on device state, device type, legal permissions, and investigative priorities.
Acquisition types:
- Logical extraction: Uses the device’s APIs and standard interfaces to collect accessible data (e.g., messages, contacts). Fast, minimally invasive, but may miss deleted or deep system artefacts.
- File system extraction: Accesses app containers and file structures beyond standard APIs, more comprehensive than logical but constrained by OS protections.
- Physical extraction (bit-for-bit): Creates a full image of device storage, including deleted content and unallocated space. This approach is the most revealing but often the most technically and legally complex (especially with modern hardware encryption).
Advanced Hardware Techniques
Chip-off and JTAG methods are used when software-level access is impossible (e.g., locked or damaged devices). They require specialized labs and must be justified, carefully documented, and defensible in court.
Cloud & Remote Acquisition
Many devices sync data to cloud services (iCloud, Google backups). When legally permissible, investigators will pursue cloud warrants or provider legal channels to acquire backups that may contain chat histories, photos, or device configurations, often critical if a device is inaccessible.
Practical decision matrix: when time is critical, perform a rapid logical extraction for volatile artefacts and then schedule deeper physical acquisition later in a controlled lab.
Step 4 – Parsing & Normalization: Turning Artefacts into Evidence
Raw extractions produce files, databases (e.g., SQLite), logs, and metadata. Parsing pulls meaningful artefacts – messages, contacts, geolocation points, media metadata; and normalizes timestamps and formats so that disparate sources can be compared.
Automated parsers + manual validation
Modern forensic platforms automate parsing of dozens of app formats, but automation can err (e.g., timezones, app-specific encodings). Human validation is critical for high-confidence findings.
Common artefacts
Call logs, SMS/MMS, app chat databases, media EXIF metadata, browser histories, system event logs, GPS/Wi-Fi traces. Each has quirks, timestamps may be stored in different formats or time zones and must be normalized for accurate timelines.
Step 5 – Timeline Reconstruction & Event Building (The Investigative Narrative)
The real power of mobile forensics is reconstructing what happened, when, and in what order. Investigators combine device artefacts with CDRs, CCTV, and OSINT to build a coherent timeline.
Normalize times and reconcile clock skews
Devices, network logs, and external sources may use different clocks. Correcting for skew is essential so events align properly. Recent academic work on timeline reconstruction formalizes this process and recommends unified terminology and rigorous methods.
High-level event building
From low-level logs (e.g., app write events) investigators infer higher-level events (conversations, movements, venue entry). This abstraction is how millions of raw events become a human-readable narrative.
Step 6 – Link Analysis & Pattern Detection
Mobile artefacts often reveal networks, who communicated with whom, when, and via which channels. Link analysis transforms contacts, frequent numbers/IDs, shared media, and co-location into visual networks.
Communication graphs
Frequency, reciprocity, and brokerage can point to organizers or intermediaries in a criminal network. Combining device links with CDRs and social media expands the network and increases confidence in identified roles.
Pattern detection
Algorithms can surface anomalous behaviour (sudden increases in contact frequency, communications blackout patterns, or coordinated movement), but analysts must verify patterns and avoid over-reliance on automated flags. Corroboration with independent sources (CCTV, bank records) reduces false positives.
Step 7 – Reporting, validation & courtroom readiness
A technically robust analysis is only valuable if it survives legal scrutiny.
Hashing & validation
Every acquisition file should be hashed (e.g., SHA-256) and logs kept to prove images haven’t changed.
Analyst notes & methodology
Document choices made (why physical extraction was not performed, why a cloud warrant was sought), tool versions, and analyst steps. Transparency builds credibility.
Explainability for non-technical stakeholders
Produce a plain-language executive summary, annotated timelines, and visuals. Prepare experts to testify clearly, focusing on methodology and the limits of inference so courts can weigh evidence appropriately.
Legal, ethical & privacy considerations
Mobile forensics sits at the intersection of public safety and personal privacy. Doing this work responsibly preserves both justice and public trust.
Warrants & proportionality
Only seek what’s necessary and legally authorized; overbroad searches invite suppression and ethical concerns. Follow jurisdictional rules and involve legal counsel early.
Minimize scope creep
If unrelated personal data appears in an extraction, migrate it to a restricted review queue and document why it will or will not be used. Clear policies for minimization protect privacy and defendable practice.
Auditability & policy
Maintain auditable trails for all decisions. Regularly review policies to reflect technology changes (e.g., new encryption, cloud architectures). Agencies that publish their policies and controls foster public trust.
Technical Challenges & Common Pitfalls
Investigators regularly face obstacles; awareness helps mitigate them:
Device & OS fragmentation
Hundreds of models, proprietary bootloaders, and hardware encryption schemes make one-size-fits-all approaches impossible. Keep specialist contacts and lab escalation paths ready.
Encrypted apps & app-specific containers
End-to-end encryption and app sandboxing require targeted parsing or cloud-forensic routes where allowed. Be prepared with legal requests for provider-held data where appropriate.
Volatile data & time sensitivity
Remote wipe or app overwrites can occur quickly. Rapid logical acquisition can preserve volatile artefacts while planning deeper extraction.
Evidence contamination during field handling
Small procedural mistakes (improper Faraday use, not recording device state) can be exploited, train and rehearse standard operating procedures frequently.
Innovations accelerating mobile forensics

The field is advancing fast; here are trends that change investigator workflows:
AI-assisted prioritization
Machine learning helps surface high-relevance artefacts (anomalous contacts, suspicious keywords) so analysts focus where it matters most. But AI outputs must be explainable and validated.
Integrated multi-source platforms
Systems that natively correlate mobile data with CDRs, CCTV, and OSINT reduce manual stitching and accelerate insight. This is where investigative value multiplies: a call, a location match, and a CCTV frame together create strong, corroborated evidence.
Cloud-first collaboration
Secure, audited cloud workspaces enable multi-jurisdiction teams to share parsed evidence and analysis without moving raw images around, improving speed while maintaining chain-of-custody controls.
Better timeline frameworks
Academic advances provide more rigorous frameworks for event reconstruction, improving consistency across examinations and aiding reproducible analysis.
Conclusion: Forensic Discipline + Human Judgment
Mobile device forensics is powerful because it combines technical rigor with investigative judgment. Devices provide signals; investigators create meaning.
Innovations in AI and integrated platforms accelerate the work, but responsibility, explainability, and legal compliance remain the foundations of trustworthy practice.
When combined, disciplined forensics and careful human interpretation deliver reliable, defensible results that serve both public safety and the rule of law.
FAQs – Frequently Asked Questions
Q: What is the difference between logical and physical extraction?
A: Logical extraction uses normal device interfaces to capture accessible data (messages, contacts) while physical extraction creates a full bit-for-bit image including deleted data and unallocated space. Physical extraction is more complete but technically and legally more complex.
Q: Can deleted messages be recovered?
A: Often yes, deleted messages may remain in unallocated space or backups. Success depends on the extraction method, time since deletion, and whether storage has been overwritten.
Q: When should investigators use a Faraday bag?
A: When the risk of remote alteration exists (e.g., remote wipe), or when preserving network state is necessary. Use with care, place chargers inside the bag if powering the device, and follow agency SOPs.
Q: How do labs validate their tools?
A: Labs maintain tool validation records, test images, and documented procedures showing tool outputs are reliable for intended purposes, as recommended by standard norms.




