The Invisible Trail Behind Every Crime
In major criminal investigations, suspects may destroy physical evidence. They may avoid CCTV cameras. They may operate through intermediaries to distance themselves from the crime.
But they almost always communicate. Behind almost every organized act, whether a homicide, kidnapping, financial fraud, or coordinated criminal activity, there is a communication trail. That trail often lives inside telecom metadata.
Call Detail Records (CDRs) frequently become the invisible thread that connects suspects to victims, reconstructs timelines, and establishes location proximity. In many field investigations, CDR analysis shifts a case from suspicion to structured evidence.
This is not theoretical or laboratory-level analysis. It is a practical investigative tool used in:
- Homicide investigations
- Organized crime cases
- Kidnapping and extortion operations
- Financial crime networks
- Terror-related investigations
For investigators, CDRs are often the first structured dataset that provides clarity when physical evidence is limited.
This blog breaks down how CDR analysis works at the field level, where it adds investigative value, and how structured telecom analytics strengthens major criminal investigations.
Key Takeaways
1. CDRs Capture Metadata, Not Conversations
They provide structured communication data without recording content.
2. Communication Patterns Reveal Coordination
Frequency, timing, and clustering often indicate organized activity.
3. Location Correlation Strengthens Evidence
Cell tower mapping supports movement reconstruction.
4. Network Mapping Exposes Hidden Links
Link analysis identifies intermediaries and core nodes.
5. Timeline Reconstruction Builds Narrative
Overlaying calls, locations, and events clarifies sequence.
6. Manual Analysis Has Limits
Large datasets require structured analytics platforms.
7. CDR Analysis Supports, Not Replaces, Investigation
It enhances investigative clarity alongside other evidence.
8. Structured Telecom Analytics Strengthens Prosecution
Clear visualizations and organized evidence improve case presentation.
What Is CDR Analysis?

Definition
CDR analysis refers to the systematic examination of Call Detail Records, metadata generated by telecom operators, to identify communication patterns, location data, and network relationships relevant to a criminal investigation.
It’s important to clarify that CDRs do not contain call recordings or conversation content. They contain metadata, structured information about communication events.
Typical CDR data fields include:
- Calling number
- Receiving number
- Date and timestamp
- Call duration
- Cell tower location used during the call
- IMEI or device identifiers
This metadata enables investigators to answer critical questions:
- Who was in contact with whom?
- When did communication occur?
- How frequently did two parties interact?
- Was a suspect’s device near a crime location?
- Did multiple devices move together?
CDR analysis transforms raw telecom logs into actionable investigative intelligence.
When Is CDR Analysis Used in Criminal Investigations?

CDR analysis is rarely used in isolation. It typically complements physical evidence, witness statements, CCTV footage, and financial records.
Below are common scenarios where it plays a decisive role:
Homicide Cases
Investigators examine:
- The victim’s last calls
- Unusual communication spikes before the incident
- Sudden silence patterns after the crime
- Device presence near the crime scene
CDR analysis often helps identify last-contact individuals and narrow suspect pools.
Kidnapping & Extortion
In abduction cases, speed is critical. CDRs assist in:
- Identifying unknown numbers contacting the victim
- Tracking ransom communication
- Locating suspect devices through tower correlation
- Mapping communication between accomplices
Telecom analysis can significantly accelerate suspect identification.
Organized Crime
Organized networks rely heavily on structured communication. CDR analysis helps:
- Detect repeated communication clusters
- Identify central command nodes
- Reveal intermediaries acting as buffers
- Establish network hierarchies
Rather than viewing isolated suspects, investigators can visualize entire criminal ecosystems.
Drug Trafficking
Drug distribution networks often operate through layered contact chains. CDR analysis supports:
- Identifying supply chain linkages
- Mapping distributor-to-retailer communication
- Detecting recurring contact timing patterns
- Establishing coordinated device movement
Financial Fraud
In financial crime investigations, telecom metadata often links otherwise disconnected actors. Investigators can:
- Connect account holders through frequent calls
- Identify shared devices
- Detect coordinated transaction timing aligned with communication spikes
Terror Investigations
In high-risk cases, CDR analysis assists in:
- Mapping communication networks
- Identifying sleeper contacts
- Detecting synchronized device movement
- Linking suspects across jurisdictions
In such cases, structured telecom analytics becomes critical for both prevention and prosecution.
Across all these scenarios, CDR analysis provides one consistent advantage: It converts invisible communication behaviour into structured investigative insight.
When handled systematically and within legal frameworks, telecom metadata becomes one of the most powerful tools available to investigators, not because it reveals conversations, but because it reveals patterns.
Step-by-Step: How CDR Analysis Works in the Field
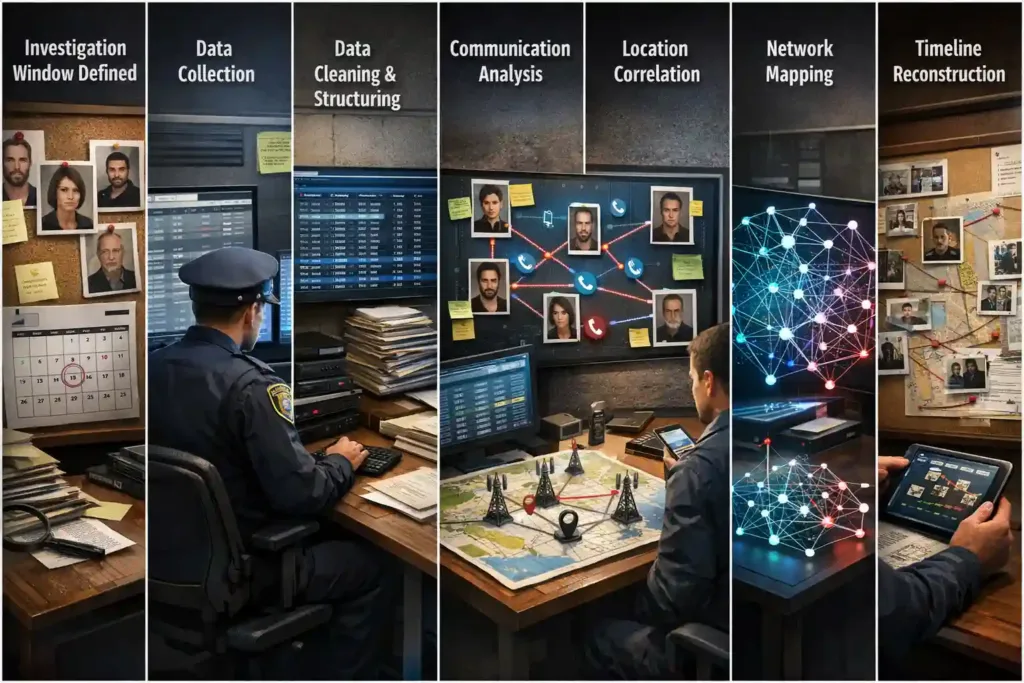
In major criminal investigations, CDR analysis follows a structured workflow. When done systematically, it converts raw telecom logs into court-admissible, intelligence-backed insight. Below is how CDR analysis typically unfolds at the field level.
Step 1: Defining the Investigation Window
Before requesting telecom data, investigators clearly define the scope. This includes:
- Incident date and time
- Primary suspects (if identified)
- Victim communication history
- Known associates and frequent contacts
The objective is precision. By narrowing the time window and relevant numbers, investigators avoid unnecessary data overload and ensure that telecom requests remain focused and legally justified.
Step 2: Data Collection from Telecom Providers
Once the investigation window is defined, law enforcement formally requests telecom records as per applicable legal procedures. Data may include:
- Call Detail Records (CDRs) for specified numbers
- Subscriber details
- IMEI-device mapping
- Tower dump data (where legally permitted and operationally relevant)
Legal compliance is critical at this stage. Requests must align with lawful interception and data access frameworks to ensure admissibility and procedural integrity.
Step 3: Data Structuring & Cleaning
Raw telecom data is often:
- Large in volume
- Unstructured across formats
- Repetitive or overlapping
Before meaningful analysis begins, normalization is required.
This typically involves:
- Removing duplicate entries
- Standardizing timestamps
- Aligning cell tower codes with geographic references
- Formatting multi-provider data consistently
Without proper structuring, pattern recognition becomes unreliable. Advanced CDR analytics platforms automate much of this process, significantly reducing manual spreadsheet dependency.
Step 4: Communication Pattern Analysis
This is where CDR pattern analysis in criminal investigation begins. Investigators examine:
- Frequency of contact between parties
- Unusual spikes in communication before the incident
- Sudden silence patterns after the crime
- Cross-linked numbers connecting suspects
Key questions include:
- Did communication increase unusually prior to the event?
- Did multiple suspects coordinate via repeated calls?
- Are unknown numbers repeatedly appearing in critical windows?
Pattern analysis often reveals coordination that is not visible through isolated call logs.
Step 5: Location Correlation
CDR location analysis for police focuses on mapping communication events to physical geography.
Investigators analyze:
- Cell tower locations used during calls
- Movement patterns over time
- Suspect device presence near the crime scene
- Co-location of multiple devices
While cell tower data does not provide GPS-level precision, it can establish presence within a coverage area and demonstrate movement consistency. When aligned with crime timelines, location correlation strengthens evidentiary narratives.
Step 6: Network Mapping
Individual call analysis is rarely sufficient in major cases. Network mapping identifies:
- Common contacts between suspects
- Hidden intermediaries
- Clustered communication groups
- Core nodes driving coordination
This is where structured link analysis tools become essential.
Platforms such as InteleLinx, designed specifically for advanced CDR analysis, convert communication logs into visual network graphs. These tools allow investigators to:
- Detect communication clusters
- Identify high-centrality nodes
- Track multi-number and IMEI associations
- Reveal device-sharing patterns
Instead of manually tracing numbers across spreadsheets, investigators gain a graphical view of the criminal communication ecosystem.
Step 7: Timeline Reconstruction
The final analytical layer overlays:
- Communication events
- Location data
- Crime timeline milestones
By synchronizing these elements, investigators can reconstruct:
- Pre-crime coordination
- Incident-time device activity
- Post-crime behaviour shifts
Timeline reconstruction often becomes pivotal during prosecution, as it provides structured, chronological evidence of interaction and movement.
High-Impact Use Case Scenarios

CDR analysis becomes most impactful when applied to real investigative contexts.
Homicide Investigation
Investigators may:
- Identify the victim’s last contact
- Detect a sudden surge in calls before the incident
- Trace suspect device movement near the crime location
- Reveal coordinated communication between accomplices
CDR evidence often helps narrow suspect pools early in the investigation.
Kidnapping Case
In abduction scenarios, speed is critical. CDR analysis supports:
- Tracking victim phone activity post-incident
- Identifying unknown recurring callers
- Mapping ransom communication chains
- Establishing suspect device proximity
Structured telecom analytics accelerates actionable intelligence during time-sensitive operations.
Organized Crime Network
Organized criminal groups rely on layered communication. CDR network mapping can:
- Detect repeated communication clusters
- Identify command-and-control nodes
- Reveal layered hierarchy structures
- Establish multi-device coordination patterns
This shifts the focus from arresting individuals to dismantling networks.
How Structured CDR Analytics Platforms Improve Investigations

Manual CDR analysis through spreadsheets becomes impractical in large, multi-accused cases.
Structured CDR analytics platforms improve investigations through:
- Automated link analysis
- Visual network graphs
- Integrated geospatial mapping
- Interactive timeline dashboards
- Multi-case correlation capabilities
- Faster pattern detection
- Reduced manual errors
Platforms such as InteleLinx support:
- Comprehensive CDR and IPDR processing across formats
- IMEI and multi-number analysis
- Geospatial mapping integration
- Single-click subject profiling
- Automated report generation
By combining communication analysis, location correlation, and visual network mapping, structured platforms convert telecom metadata into clear investigative intelligence.
Importantly, these systems do not replace investigators. They enhance analytical speed, reduce manual workload, and improve clarity in high-stakes criminal investigations.
In major cases, that clarity can define the difference between suspicion and structured proof.
Conclusion
In major criminal investigations, communication patterns often reveal what physical evidence cannot. Call Detail Records do not capture conversations, but they capture behavior. And behavior, when analyzed systematically, tells a story.
From narrowing suspect pools to reconstructing timelines and mapping hidden networks, CDR analysis transforms raw telecom metadata into structured investigative intelligence. When supported by advanced analytics platforms, investigators can move beyond manual spreadsheets and uncover coordinated activity with greater clarity and speed.
CDR analysis is not a standalone solution. It works alongside physical evidence, witness statements, CCTV, and financial records. But in complex, multi-accused cases, it frequently becomes the backbone of structured proof, turning invisible communication trails into actionable insight.
Frequently Asked Questions (FAQ)
1. What is CDR analysis in criminal investigations?
CDR analysis is the examination of telecom metadata to identify communication patterns, locations, and network relationships relevant to a case.
2. Does CDR include call recordings?
No. CDRs contain metadata such as numbers, timestamps, duration, and tower locations, not call content.
3. Howaccurateis cell tower location analysis?
Cell tower data establishes presence within a coverage area. It is not GPS-level precise but can support movement correlation.
4. Can CDR analysis prove someone was at a crime scene?
It can indicate device presence within a tower range near a crime scene, especially when supported by additional evidence.
5. How do investigators map communication networks?
Through link analysis tools that visualize connections between numbers, devices, and shared contacts.
6. Is CDR analysis admissible in court?
When obtained and processed under proper legal procedures, CDR-based evidence can support prosecution.
7. Why is structured CDR software important?
It reduces manual errors, accelerates pattern detection, and enables visualization of complex communication networks.




