According to the United Nations Office on Drugs and Crime, between $800 billion and $2 trillion is laundered through the global financial system every year, and only 1% of those illicit financial flows are ever detected and seized by authorities.
One percent.
AML compliance costs banks and financial institutions over $60 billion annually worldwide, yet the financial crime it is designed to stop continues largely unimpeded. The money moves. The networks operate. The compliance machinery hums. And the gap between what the system costs and what it actually stops remains, by any measure, enormous.
In India, the picture is equally stark. Over 5,000 cases were registered under the Prevention of Money Laundering Act in the last decade, but only 40 convictions were made; source: The Hindu. And India’s FATF 2024 Mutual Evaluation flagged a critical structural bottleneck: a “large backlog of pending cases” that severely hampers AML prosecutions, with the report noting that “prosecutions and convictions have started to increase, but the backlog of pending cases remains considerable.”
This is not a resourcing problem alone. It is fundamentally an investigative capability problem, and it’s what this blog addresses directly.
Key Takeaways
- The money always leaves a trail, money laundering is not invisible, it is analytically difficult; every transaction generates data that, correlated correctly, reveals the network behind it.
- The 1% detection figure is an analytical gap, not a data gap, the evidence exists in financial records; the problem is whether the investigative infrastructure can read it at speed and scale.
- AML investigations have five distinct stages, each with its own analytical requirements and its own failure points; technology gaps at any stage compromise the full investigation.
- Rule-based transaction monitoring is the weakest link, it generates high false positive volumes while missing the network-level patterns that sophisticated laundering operations actually use.
- Network analysis is the single most impactful upgrade, seeing the relationships between entities, not just the transactions between accounts, is what surfaces criminal infrastructure.
- Beneficial ownership is where sophisticated laundering hides, shell companies, layered structures, and nominee directors are designed to defeat account-level investigation; they require entity-graph analysis to unravel.
- The India-specific context matters, PMLA obligations, FIU-IND reporting, hawala networks, real estate layering, and UPI-based structuring create a distinct investigation landscape that generic global AML tools were not built for.
What AML Investigation Actually Involves

Anti-money laundering investigation is the process of identifying, tracing, and building a prosecution-ready evidentiary case around illicit financial flows, from the first suspicious signal through the complete network of entities, transactions, and relationships to the criminal enterprise at the centre.
It’s not the same as AML compliance. Compliance is about meeting regulatory obligations, filing CTRs and STRs, maintaining KYC records, passing audits. Investigation is about following the money to its source and building a case that holds up in court.
The distinction matters because the skills, tools, and analytical infrastructure required for investigation are substantially different from those required for compliance. An institution that is fully compliant, filing every STR on time, maintaining clean KYC records, may simultaneously have almost no capability to conduct the deeper investigation that turns a suspicious transaction report into a prosecution.
Most AML technology investment in India has gone into compliance infrastructure. The investigation capability gap is where the 1% detection rate lives.
The Five Stages of an AML Investigation, And Where Each One Breaks Down

Stage 1: Detection, From Transaction Alert to Investigable Case
The investigation begins with a signal, a transaction monitoring alert, a suspicious transaction report, a tip from another agency, or a pattern flagged by a compliance officer. At this stage, the question is: is this a genuine investigation lead, or one of the thousands of false positives that compliance systems generate daily?
Where it breaks down: Most transaction monitoring systems are rule-based, they flag transactions that exceed defined thresholds or match specific patterns. The false positive rate is high; most estimates suggest that 90–95% of AML alerts generated by rule-based systems are ultimately false positives. Compliance teams spend the majority of their time reviewing alerts that lead nowhere, while genuine laundering operations, specifically designed to stay below thresholds and avoid known patterns, generate no alert at all.
The detection problem is not sensitivity. It is precision: generating alerts that are actually indicative of suspicious activity rather than simply threshold breaches.
Stage 2: Triage, Assessing Whether to Investigate Further
A flagged alert reaches a compliance officer or investigator. The question is now: does this warrant deeper investigation, escalation to the FIU, or closure as a false positive?
This triage decision requires context, what do we know about this customer, this account, this counterparty? How does this transaction fit into the customer’s overall profile? Are there prior alerts on this account or related entities? Is there broader intelligence that contextualises this transaction?
Where it breaks down: Triage decisions made without access to the full context of an account’s history, its network of related entities, and any prior intelligence about the parties involved are unreliable. Investigators making triage decisions from incomplete pictures close cases that should be opened and escalate cases that lead nowhere. The quality of triage is directly proportional to the breadth of accessible intelligence at the point of decision.
Stage 3: Investigation, Building the Financial Crime Picture
An alert has been escalated. Now the investigation proper begins: tracing the funds, mapping the network, identifying the entities involved, and establishing the financial crime picture in sufficient detail to support either an STR to FIU-IND or referral to the Enforcement Directorate for prosecution.
This is the analytically intensive stage. It involves transaction tracing, following funds from their entry point through the full layering chain to their destination. Network mapping, identifying the entities, accounts, companies, and individuals connected to the suspicious activity and their relationships to each other. Beneficial ownership investigation, peeling back the layers of shell companies, nominee directors, and complex structures to identify who actually controls and benefits from the suspicious accounts and transactions.
Where it breaks down: This stage is where the investigation capability gap is most acute. Following funds through multiple hops, across multiple institutions, through layered corporate structures, involving multiple currencies and geographies requires analytical infrastructure that most Indian financial institutions and investigation agencies do not currently have. The evidence is in the financial records. The ability to correlate it, visualise it, and turn it into a coherent narrative is the gap.
Stage 4: Documentation, Building the Prosecution-Ready Case
The investigation has developed sufficient evidence to support a case. Now that evidence must be documented, structured, and presented in a form that meets the evidentiary requirements of the judicial process, supporting an STR to FIU-IND, providing intelligence to the Enforcement Directorate, or building a prosecution brief.
Where it breaks down: Documentation of complex financial crime cases is time-intensive and error-prone when done manually. A multi-entity, multi-transaction money laundering case may involve hundreds of data points across multiple data sources. Turning this into a coherent, auditable, court-ready case without AI assistance is slow, and the risk of documentation gaps that create evidentiary vulnerabilities is significant.
Stage 5: Intelligence Sharing, Enabling Cross-Institution and Cross-Agency Correlation
A case at one institution may be a fragment of a larger network visible across multiple institutions. Intelligence about the investigation, suitably anonymised and structured, needs to flow to FIU-IND, to the Enforcement Directorate, to other affected institutions, and potentially to international counterpart agencies for cross-border elements.
Where it breaks down: The quality of intelligence that flows from institutions to FIU-IND is variable. Low-quality, insufficiently detailed STRs, filed to meet a compliance obligation rather than to genuinely support investigation, are a documented problem in India’s AML ecosystem, flagged explicitly in FATF assessments. The investigation that generated the STR needs to be deep enough to produce actionable intelligence, not just a checkbox filing.
The Three Analytical Capabilities That Transform AML Investigation
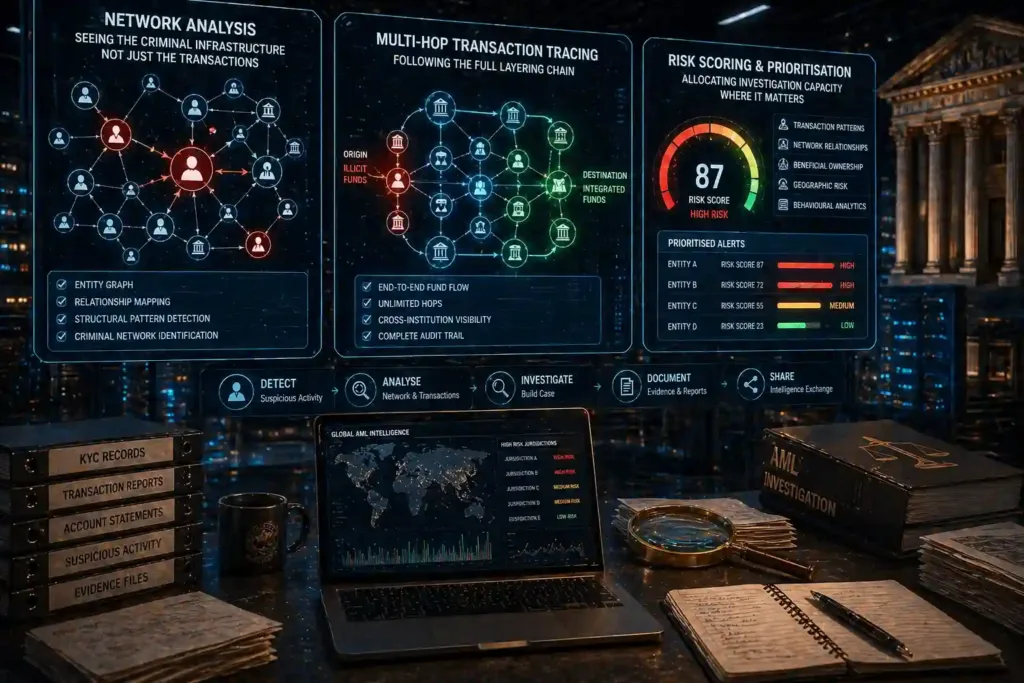
1. Network Analysis,Seeing the Criminal Infrastructure, Not Just the Transactions
Money laundering is a network phenomenon. No individual transaction is the crime, the crime is the structure of connected entities, accounts, and flows that collectively move and disguise illicit funds. Investigating at the transaction level, evaluating accounts individually against thresholds, will never surface a network that is specifically designed to distribute activity across many accounts, each individually below any alert threshold.
Network analysis changes the unit of investigation from the transaction to the entity graph. By mapping the relationships between accounts, individuals, companies, and transactions, and analysing the structural properties of those relationships, investigators can identify the criminal network regardless of whether any individual transaction triggers a rule.
The signatures of criminal financial networks are structurally distinctive: accounts that receive from multiple unrelated sources and transfer to common destinations; circular fund flows between entities with no legitimate commercial relationship; corporate ownership structures with nominee directors appearing across multiple apparently unrelated entities; transaction velocity patterns inconsistent with the declared business of the involved entities.
These patterns are invisible at the account level. They are readily apparent in a well-constructed entity graph with AI-powered pattern detection.
2. Multi-Hop Transaction Tracing,Following the Full Layering Chain
Layering, the stage of money laundering where funds are moved repeatedly between accounts and entities to obscure their origin, is specifically designed to defeat transaction-level monitoring. Each individual hop in the layering chain may appear legitimate. The full chain reveals the criminal structure.
Following funds through four, five, or ten hops across multiple accounts, institutions, and time periods manually is operationally impossible at investigation scale. AI-powered multi-hop transaction tracing automates this, tracking funds through the full chain regardless of the number of transfers or the time elapsed between them, and presenting the complete path from origin to destination in a form that supports both investigation and evidentiary documentation.
3. Risk Scoring and Prioritisation,Allocating Investigation Capacity Where It Matters
Not all suspicious activity is equally suspicious. An AI-powered risk scoring system that continuously evaluates entities and transactions against the full picture of their behaviour, transaction patterns, network relationships, beneficial ownership, geographic risk, and declared vs. actual activity, enables investigation teams to prioritise their capacity on the highest-risk cases rather than reviewing every alert with equal depth.
This is the direct answer to the false positive problem: not reducing sensitivity, but improving precision, so that the alerts that reach investigators are the ones most likely to represent genuine financial crime.
The India Context: What Investigators Here Are Actually Dealing With
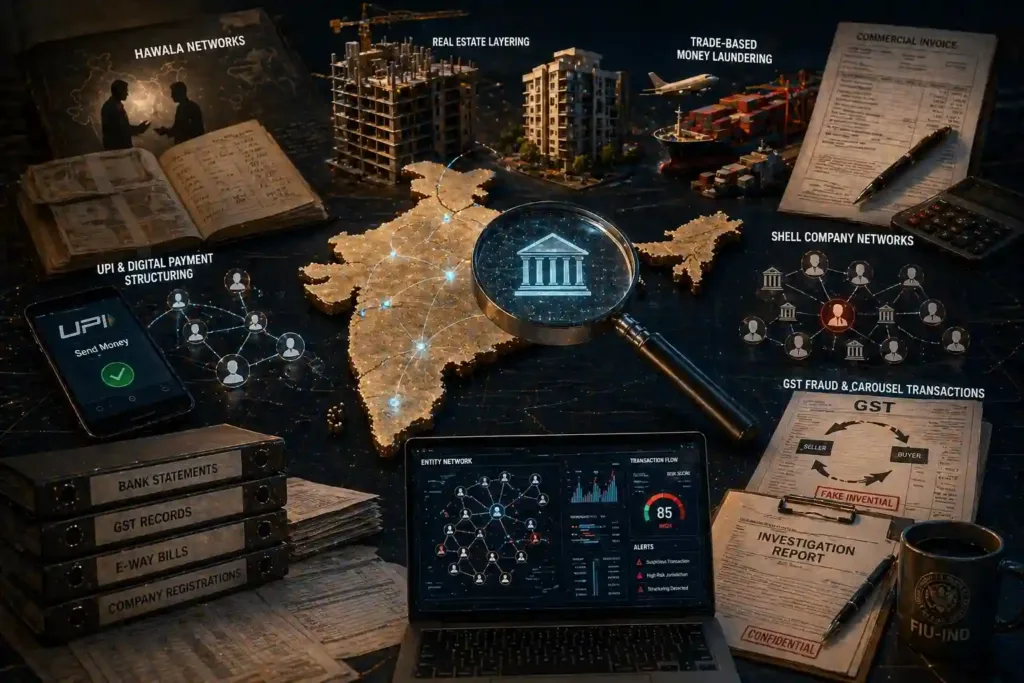
Effective AML investigation in India requires understanding the specific laundering typologies that are prevalent in the Indian financial context, not just applying global frameworks built for Western financial systems.
Hawala networks
India’s hawala system, informal value transfer outside the formal banking system, remains a significant channel for moving illicit funds, particularly in cross-border contexts. Hawala transactions leave minimal financial records and require intelligence-based investigation approaches that complement formal financial data analysis.
Real estate layering
Property transactions remain a primary layering mechanism for high-value money laundering in India. The integration of property registry data, stamp duty records, and company registration data with financial transaction analysis is essential for investigating real estate-linked laundering.
Trade-based money laundering
Over- and under-invoicing of trade transactions, manipulating the value, quantity, or quality of goods in cross-border trade to move value, is a significant and under-investigated typology in the Indian context.
UPI and digital payment structuring
The growth of UPI has given laundering networks a new structuring tool, small, high-velocity transfers across multiple accounts that collectively move significant sums below any individual reporting threshold. Detection requires analysis of UPI transaction patterns, not just traditional banking records.
Shell company networks
Layered corporate ownership, multiple shell companies with nominee directors, registered at the same addresses, with circular ownership structures, is used to obscure beneficial ownership in both domestic and cross-border laundering operations. Investigation requires entity-graph analysis that correlates company registration data, directorship records, and financial transaction data simultaneously.
GST fraud and carousel transactions
Fake invoicing, circular billing, and carousel fraud, where goods are invoiced repeatedly between connected entities to generate fraudulent GST refund claims, represent a significant financial crime typology with a direct link to money laundering. Detecting these requires correlation of GST transaction data, e-way bill records, and bank statement data in a single analytical environment.
Prophecy Eagle I: Financial Crime Analytics Built for the Full Investigation Workflow

Prophecy Eagle I is Innefu’s big data analytics platform for financial fraud detection and AML investigation, designed to address the analytical gaps across all five investigation stages described above.
Network analysis across multiple financial datasets
Prophecy Eagle I ingests and correlates bank statements, GST transaction data, company registration records, e-way bill data, vehicle ownership records, and property data, analysing the full entity graph to surface criminal network structures that are invisible in account-level analysis. The system automatically identifies clusters of connected entities with suspicious structural properties and flags them for investigation.
Multi-hop transaction tracking
The platform tracks financial transactions through multiple intermediary accounts and entities to uncover the full layering chain, following funds from point of entry through every subsequent transfer to final destination, regardless of the number of hops or the time elapsed. This is the core analytical capability for investigation Stage 3.
Cyclical transaction detection
Prophecy Eagle I automatically identifies recurring and circular transaction patterns, the fund flows that travel through chains of entities and return to approximate origin, simulating legitimate commercial activity while actually laundering funds. This addresses the carousel fraud and circular billing typologies specific to the Indian context.
Mule account detection through image analytics
The platform maintains facial libraries of known financial absconders and fraudsters, cross-referencing new account application photographs to flag duplicate identity usage, catching mule account infrastructure at the onboarding stage before it becomes operational. For a deeper treatment of mule account detection specifically, see: Mule Account Detection →
Structuring and smurfing detection
Prophecy Eagle I identifies coordinated deposit patterns across multiple accounts designed to stay below reporting thresholds, the structuring behaviour that rule-based threshold monitoring is structurally unable to detect. For a detailed treatment of smurfing detection, see: Smurfing Detection AML →
360-degree entity profiling with dynamic risk scoring
Every entity in the system, individual or corporate, carries a continuously updated risk profile drawn from transaction behaviour, network relationships, beneficial ownership analysis, and behavioural anomalies. Risk scores prioritise investigation capacity toward genuinely high-risk cases, reducing the false positive burden that undermines most AML compliance operations.
GST, bank statement, and e-way bill correlation for trade-based laundering
The platform’s integration of GST transaction data and e-way bill records alongside bank statement analysis directly addresses the trade-based money laundering and carousel fraud typologies prevalent in India, an investigation capability gap that most global AML platforms do not address.
No internet connection required
All AI models are inbuilt and run within the institution’s own infrastructure. Investigation data never leaves the controlled environment, critical for financial institutions, revenue intelligence agencies, and enforcement bodies handling sensitive case data under regulatory and legal obligations.
Learn more about Prophecy Eagle I →
Frequently Asked Questions
1. What is an AML investigation?
An AML (anti-money laundering) investigation is the process of identifying, tracing, and building an evidentiary case around suspected money laundering activity, from the initial suspicious signal through the complete network of entities, transactions, and relationships involved. It goes beyond compliance reporting (filing STRs) to include active financial intelligence work: following the layering chain, mapping beneficial ownership, building prosecution-ready documentation, and contributing actionable intelligence to law enforcement and the Financial Intelligence Unit.
2. What are the stages of a money laundering investigation?
A money laundering investigation typically progresses through five stages: detection (identifying the suspicious signal from transaction monitoring or other sources), triage (assessing whether the signal warrants deeper investigation), investigation (tracing funds, mapping the network, establishing beneficial ownership), documentation (building the prosecution-ready evidentiary record), and intelligence sharing (filing quality STRs with FIU-IND and providing intelligence to enforcement agencies). Technology gaps at any stage compromise the effectiveness of the full chain.
3. What is the difference between AML compliance and AML investigation?
AML compliance refers to meeting regulatory obligations, KYC, transaction monitoring, CTR and STR filing, record keeping, and passing regulatory audits. AML investigation refers to the active analytical work of following financial crime evidence to its source and building a case. An institution can be fully compliant while having minimal investigation capability. The 1% detection rate for illicit financial flows reflects this gap: compliance infrastructure is widespread; genuine investigation capability is not.
4. Why do most AML systems generate so many false positives?
Most transaction monitoring systems are rule-based, they flag transactions that breach defined thresholds or match specific known patterns. Money laundering operations are specifically designed to stay below these thresholds and avoid known patterns, so rule-based systems systematically miss the activity they are designed to catch while generating large volumes of alerts on legitimate transactions that coincidentally match a monitoring rule. AI-powered systems that evaluate behavioural patterns and network relationships rather than threshold rules generate substantially fewer false positives while detecting the network-level patterns that rule-based systems miss.
5. What is beneficial ownership in AML investigation and why does it matter?
Beneficial ownership refers to the natural person or persons who ultimately own or control an entity, the real human being who benefits from an account or company, as distinct from the nominee directors, shell companies, or complex ownership layers that may stand between them and the asset. Money laundering through corporate structures specifically exploits the beneficial ownership gap: by placing illicit funds in companies with obscure or layered ownership, criminals create distance between themselves and the funds. AML investigation must penetrate these structures to identify the actual beneficial owner, which requires entity-graph analysis that correlates company registration data, directorship records, and financial transaction data simultaneously.
6. What is trade-based money laundering and how is it detected?
Trade-based money laundering involves manipulating the value, quantity, or quality of goods in import/export transactions to transfer value across borders while appearing to conduct legitimate trade. Over-invoicing, under-invoicing, multiple invoicing of the same goods, and falsely described shipments are common techniques. Detection requires correlation of trade documentation, customs records, GST filings, e-way bill data, and bank statement data, identifying inconsistencies between declared trade values and actual financial flows. This is a significant typology in the Indian context that most global AML platforms are not configured to address.
7. What should a quality STR to FIU-IND contain?
A quality STR should contain sufficient detail to generate actionable intelligence, not just a description of the suspicious transaction, but the investigation context: the full transaction history supporting the suspicion, the entity relationships identified, any beneficial ownership analysis conducted, the specific money laundering typology suspected, and any corroborating information from other data sources. Low-quality STRs that contain only the triggering transaction with minimal context create a compliance record without generating investigative value. The FATF 2024 evaluation of India specifically noted the need for improvement in STR quality across reporting entities.




