How Argus Uncovered a Multi-Layered Digital Investment Fraud Network
From OTP interception and shell accounts to international handlers and coordinated money movement.
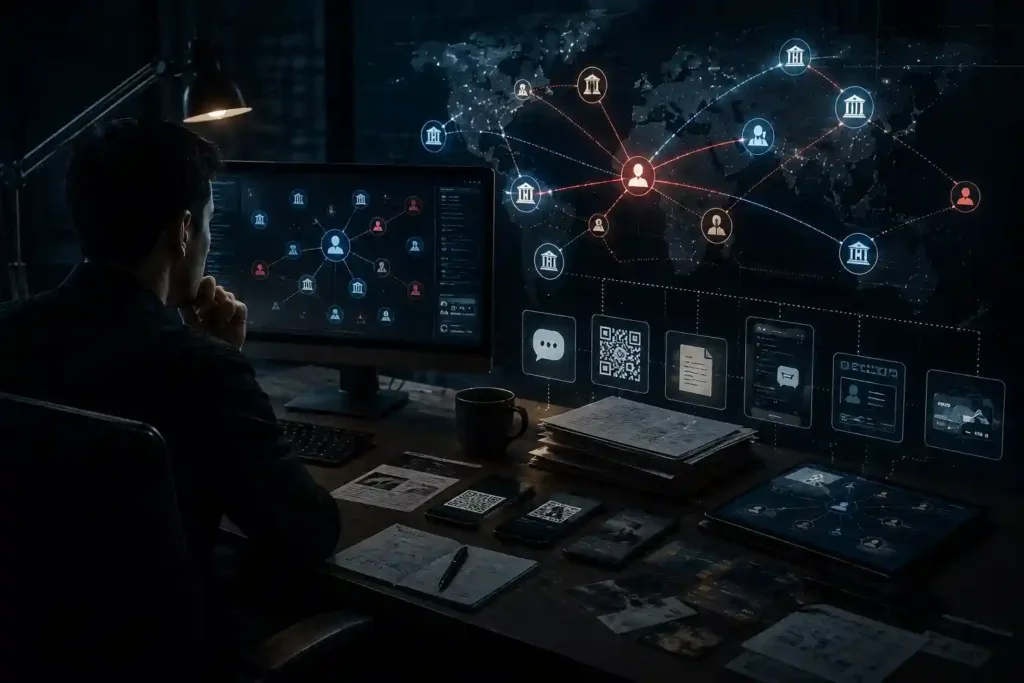
The Approach
By correlating chats, QR records, screenshots, account details, and transaction references, using Argus the investigators uncovered hidden operational relationships across the network.
Advanced keyword intelligence, OCR-based extraction, timeline reconstruction, and link analysis helped expose:
- OTP interception workflows
- Operational coordination between suspects
- Financial routing patterns
- Cross-border communication channels
- Hidden references embedded within coded language
Challenges
- OTP interception through malicious mobile applications
- Cross-border coordination with overseas handlers
- Layered financial movement through multiple accounts and entities
- SIM procurement networks designed to conceal identities
- Structured laundering workflows using QR systems and payment gateways
- Fragmented communication spread across chats, media files, and transaction records


What Argus Uncovered
- A coordinated digital fraud ecosystem operating across multiple regions
- OTP-forwarding infrastructure enabling remote account access
- International handlers linked to Dubai and other foreign locations
- Organized laundering workflows involving shell entities and payment gateways
- Coded operational language used to conceal financial movement
- Structured communication between operators, intermediaries, and financial handlers
Key Results
Cross-Border Coordination Identification
Established direct operational links between domestic suspects and international handlers connected to Dubai and other overseas locations.
Fraud Infrastructure Exposure
Uncovered the operational ecosystem behind the fraud, including OTP interception tools, SIM networks, payment gateways, and shell entities.
Multi-Source Intelligence Correlation
Connected fragmented chats, media files, financial artefacts, and communication records into a unified intelligence picture.
Financial Flow Reconstruction
Mapped suspicious fund movement across accounts, entities, QR systems, and laundering channels used to circulate fraudulent proceeds.
